Introduction to Microsoft Global Secure Access (GSA)
Introduction
A new star is on the horizon: Global Secure Access. As part of the identity security portfolio of Microsoft Entra, GSA is the new network security component to provide holistic security.
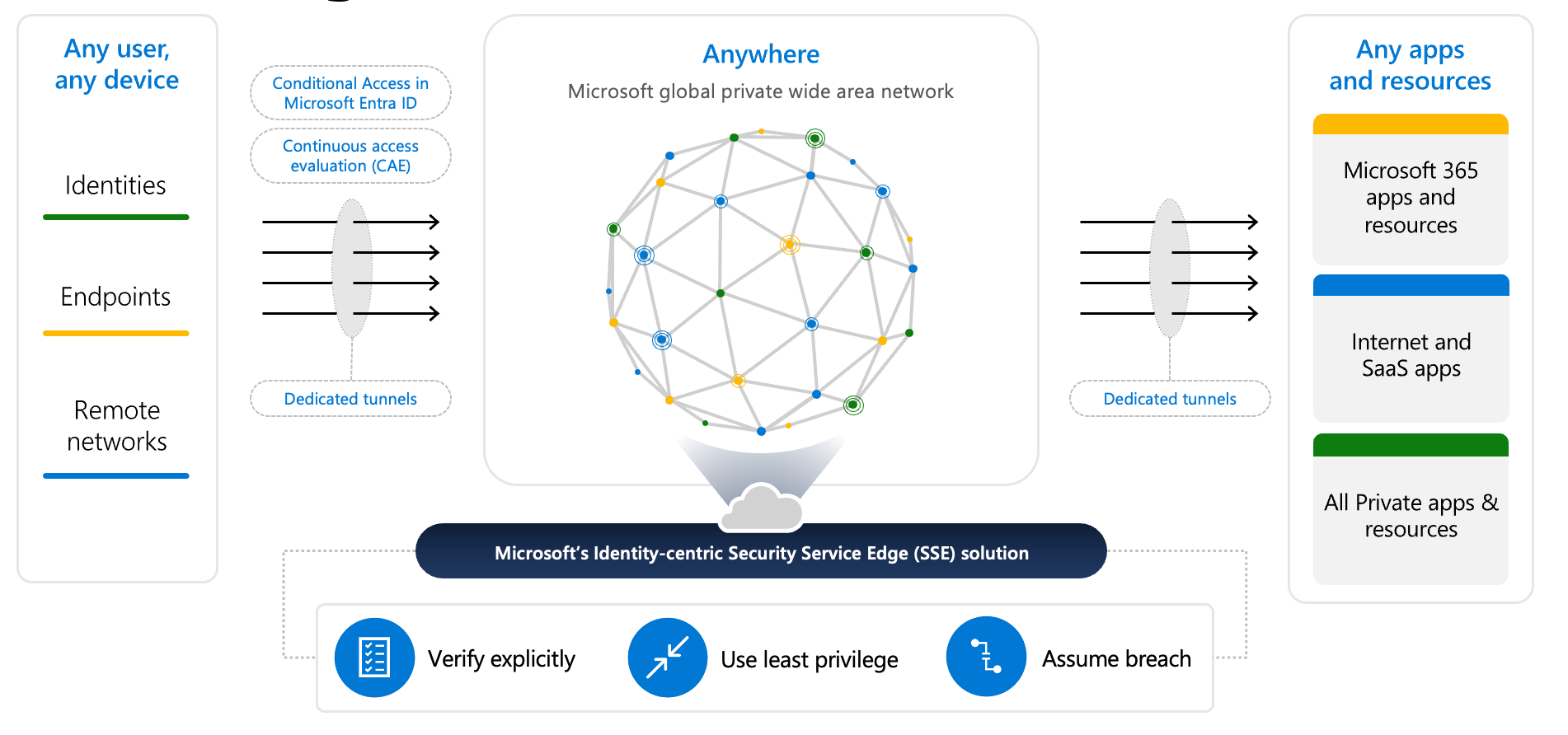
Global Secure Access in Microsoft Entra combines Internet Access and Private Access based on Zero Trust principles. It provides secure access to SaaS apps, the Internet, and private resources, protects users and data through various security components, and enables location-independent access to internal resources. Delivered via Microsoft's global network, it optimizes both security and performance and integrates into Microsoft Entra Security.
Why I like GSA
- Everything is integrated in the Microsoft ecosystem for a holistic security architecture
- Provide access to on-premises apps without additional 3rd party software and secure web traffic to the Internet
- The setup and configuration is very easy
- No maintenance tasks and continuous improvements made by Microsoft 😉
Identity-centric SSE solution
SSE 🌐
Microsoft's Network Security Service Edge enforces security policies like threat protection and access control directly at the edge, near the user, without requiring traditional networking security tools. It runs on Microsoft's global network with 190+ edge sites, providing low-latency, high-performance connections and secure access to apps and resources anywhere in the world.
Objectives 🎯
- Strengthen security by identity-driven access
- Networking, but cloud-native, aiming to rise security by:
- Applying policy profiles / routing traffic
- Set web filtering policies
- Connect with Conditional Access policies to apply access controls
- Cross over boundaries from corporate/private networks and public
- Leverage Microsoft's global network backbone for optimized connectivity
- Provide a seamless user experience
Use Cases
The following use cases are widespread across customers and their GSA usage:
- VPN > RDP with Conditional Access + modern authentication to on-premises servers
- Restrict common web content categories
- Require compliant device to access network resources (Signal in CA)
- Limit Internet network access on specialized endpoints
- Monitor network traffic and apply restrictions
Security 🔐
- The whole new product is part of Entra and seamlessly integrates into ID protection and Conditional Access to provide secure authentication, apply tenant restrictions or to detect (risk) signals and correlate activity data, based on the principles of Zero Trust
- The Global Secure Access client for Windows, macOS, Android and iOS/iPadOS is an agent that can monitor and route network traffic over the Microsoft backbone and apply controls
- Or configure a remote network where your network customer premises equipment (CPE) connects to the Global Secure Access service through an IPSec tunnel (with this no client installation is needed but dependent on the network)
- Defender for Cloud Apps gives further insights as cloud security access broker (CASB) between the communication of your identities and cloud apps and allows for policies regarding app governance
Access Channels 🚦
The traffic from three app/resource channels can be differently treated:
- Microsoft 365 - all traffic to Microsoft network endpoints
- Private access - traffic to on-premises hosted apps
- Internet access - traffic to any other network/the Internet
Components
| Term | Description | Microsoft solution |
|---|---|---|
| Software-defined wide area network (SD-WAN) | Technology that optimizes and manages multiple sources of network connectivity to enhance the performance, efficiency, managebility and security of wide area networks | Entra SSE |
| Secure web gateway (SWG) | Network perimeter protection that filters traffic for particular networks | Micrsooft Entra Internet Access |
| Cloud access security broker (CASB) | Security solution that provides visibility and control over data and applications as they move between an organization's on-premises infrastructure and cloud environments | Microsoft Defender for Cloud Apps |
| Firewall as a service (FWaaS) | Cloud-based security solution that delivers firewall functionality, such as traffic filtering and network protection and policies | Microsoft Entra Internet Access |
| Zero Trust Network Access (ZTNA) | Security framework that requires zero trust, least privileged, all identities must be authenticated, authorized, and continuously validated before being granted access to company private applications and data | Microsoft Entra Private Access |
Prerequisites
| Prerequisite | Description |
|---|---|
| Licensing | - Entra Suite - Or standalone: - Entra Private Access - Entra Internet Access ❌ Additional license required, not included in E5 or Entra ID P2. |
| Network Endpoints | Microsoft 365 endpoints |
| Devices | - Entra joined or registered - Latest versions of: - Windows 10/11 (incl. Windows 365, no AVD multi-session) - macOS - Android - iOS/iPadOS |
| Roles | - Global Secure Access Admin or Global Admin |
| Browser Support | - Microsoft Edge or Google Chrome recommended |
| Client Software | - Global Secure Access client installed |
| Conditional Access | - Optional, but recommended |
Conditional Access Integration
Conditional Access is used to activate and enforce GSA channel profiles. It controls the enforcement of Private Access and Internet Access, allowing familiar policies to be applied.
- Different Conditional Access policies can be created to target specific user groups and apply varying security standards
- Private Access is handled in Conditional Access as a target app (GSA-enabled)
- Internet Access is handled as a traffic profile and enforced through session control
Read more about Conditional Access:

Internet Access
With Internet Access from Global Secure Access, access to internet resources and apps can be secured, similar to using a proxy. The following can be achieved:
- Allow or block website access using security policies and Conditional Access
- Apply web content filtering policies based on categories
- Monitor traffic
Setup & prerequisites
Ensure the following things as prerequisites:
- Global Secure Access Administrator role
- Entra joined Windows test device
These are the key steps to setup:
- Enable GSA for the tenant (if not already done)
- Enable Internet Access Profile
- Create security profiles & web content filter rules
- Install Global Secure Access Client
- Combine with Conditional Access
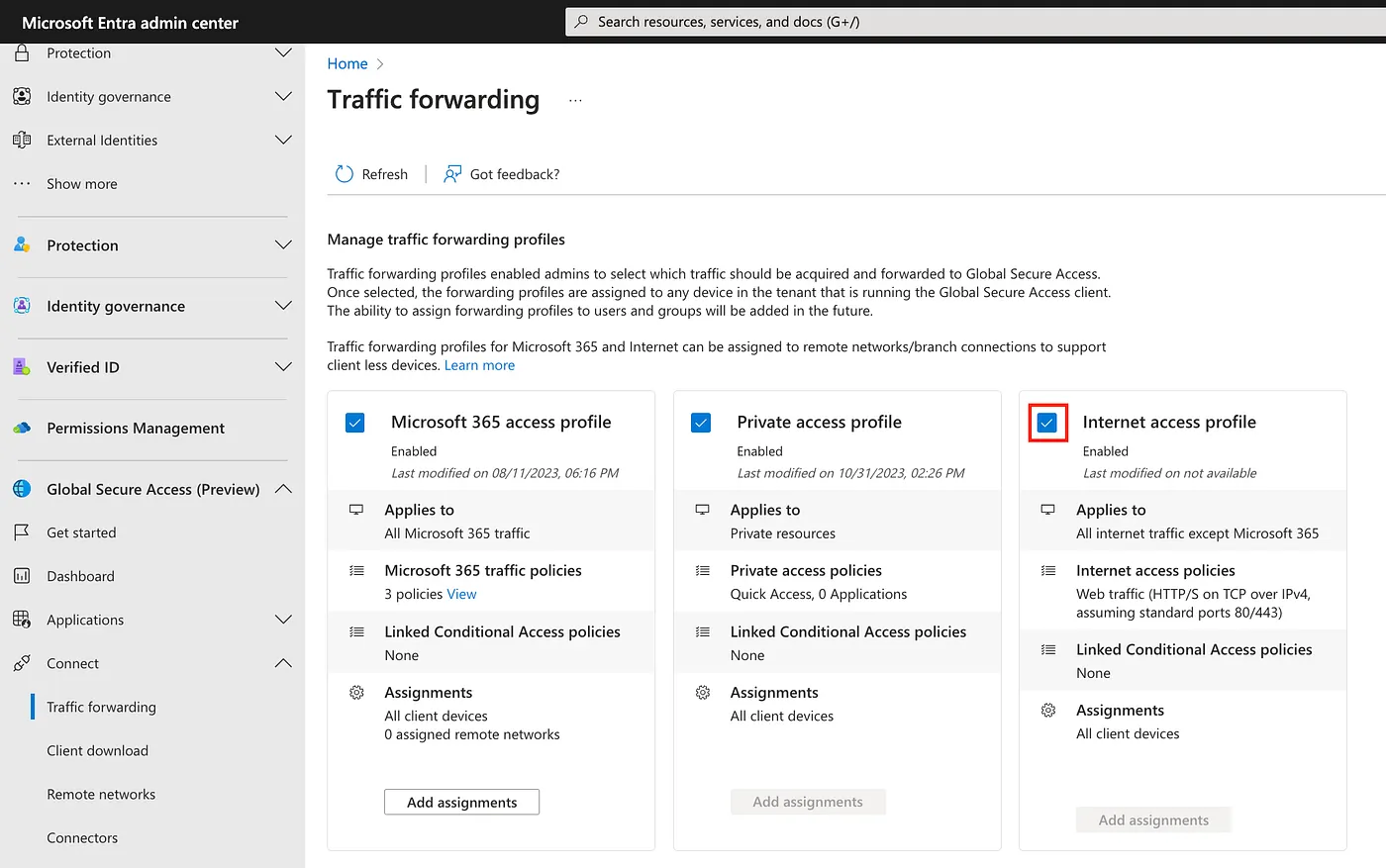
1. Enabling Internet Access Profile
Go to Entra > GSA > Connect > Traffic forwarding and enable the Internet Access on the tenant level as feature
2. Create security profiles & web content filter rules
The effective configuration needs to be done at Entra > GSA >
- Security profiles — policy profiles that are assigned to Conditional Access, these contain rules from web content filtering policies (unique priority defines which one takes precedence)
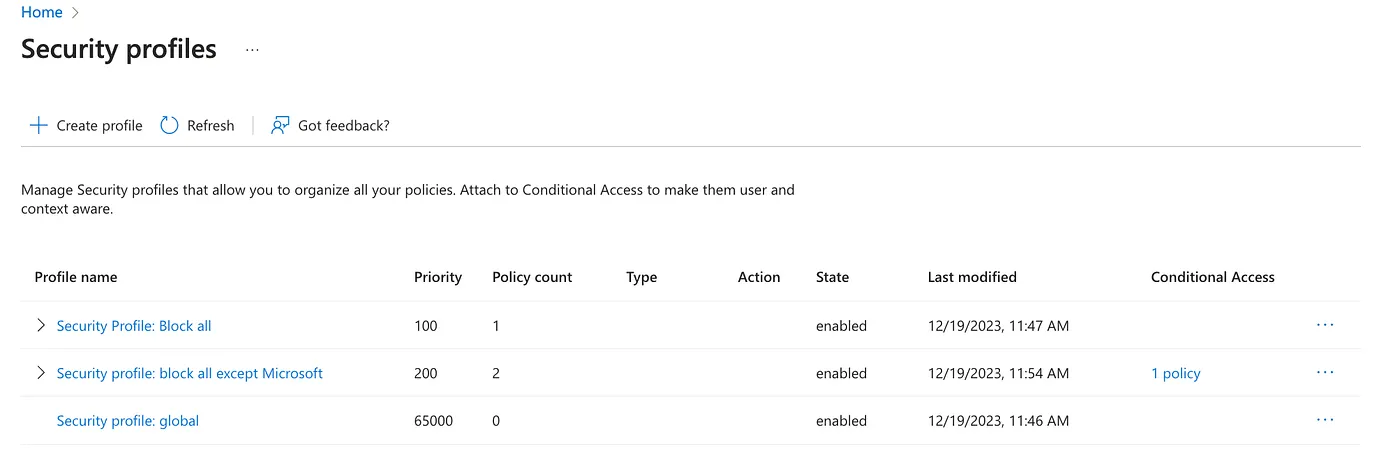
The configuration of these is pretty simple, all you need to do is:
- Create a security profile, choose priority (❗️ Priority 65000 means, that the policy is globally applied and is effective when GSA uses Internet traffic, no linking to Conditional Access policies is needed)
- Link existing web content filtering policies or create new ones
- If you create a new one, specify the action type, either “allow” or “block” and create one or multiple rules within it — again you can choose between a predefined category by Microsoft or enter a custom FQDN (supporting wildcards)
Private Access
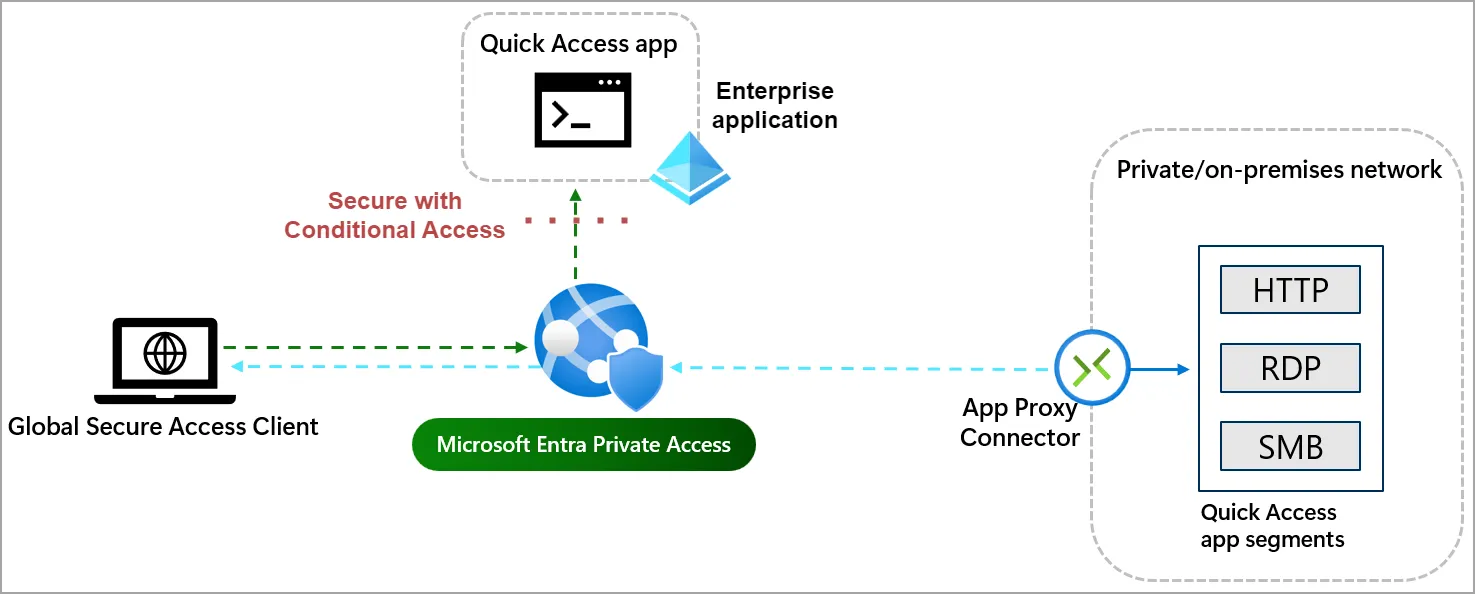
With Private Access from Global Secure Access, access to internal resources and apps is enabled—similar to VPN access, but app-based and fully integrated into Entra ID.
- Enables app-specific access from any network to on-premises resources
- Modernizes and secures authentication and access for legacy apps using Conditional Access
Steps
- Enable Microsoft Entra Private Access
- Download & install the Global Secure Access client
- Configure Quick Access
- Implement Conditional Access policy
Setup & prerequisites
As a prerequisite, please make sure you install a Connector Service. (also known as Azure AD Application Proxy connector) It is important that this connector has connectivity to the internal resource (essentially IP or FQDN) which we specify later.
1. Enable Microsoft Entra Private Access
Go to the Microsoft Entra admin center and expand the Global Secure Access pane. You may need to enable this feature for the tenant first.
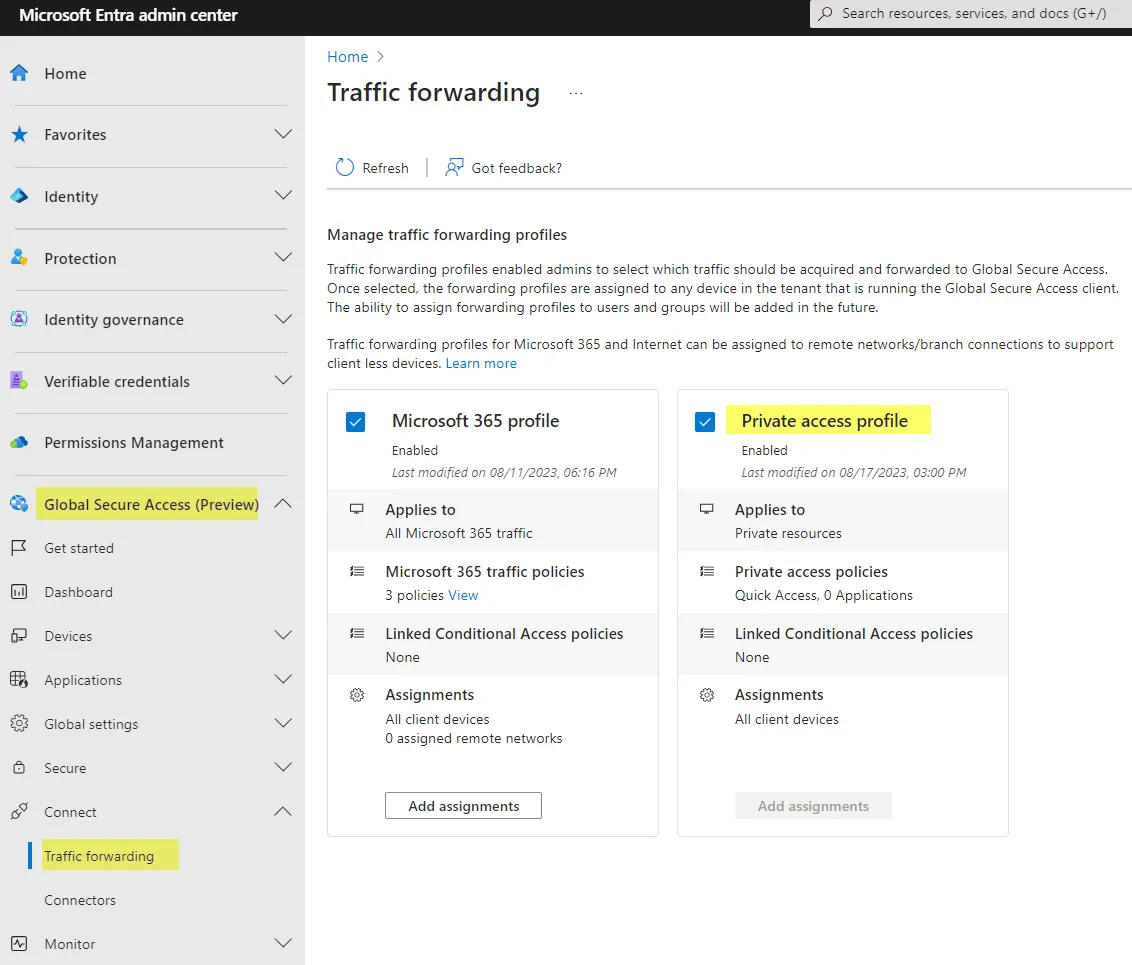
Go to Traffic forwarding and make sure the Private access profile is enabled. (Also for troubleshooting you can disable & enable again)
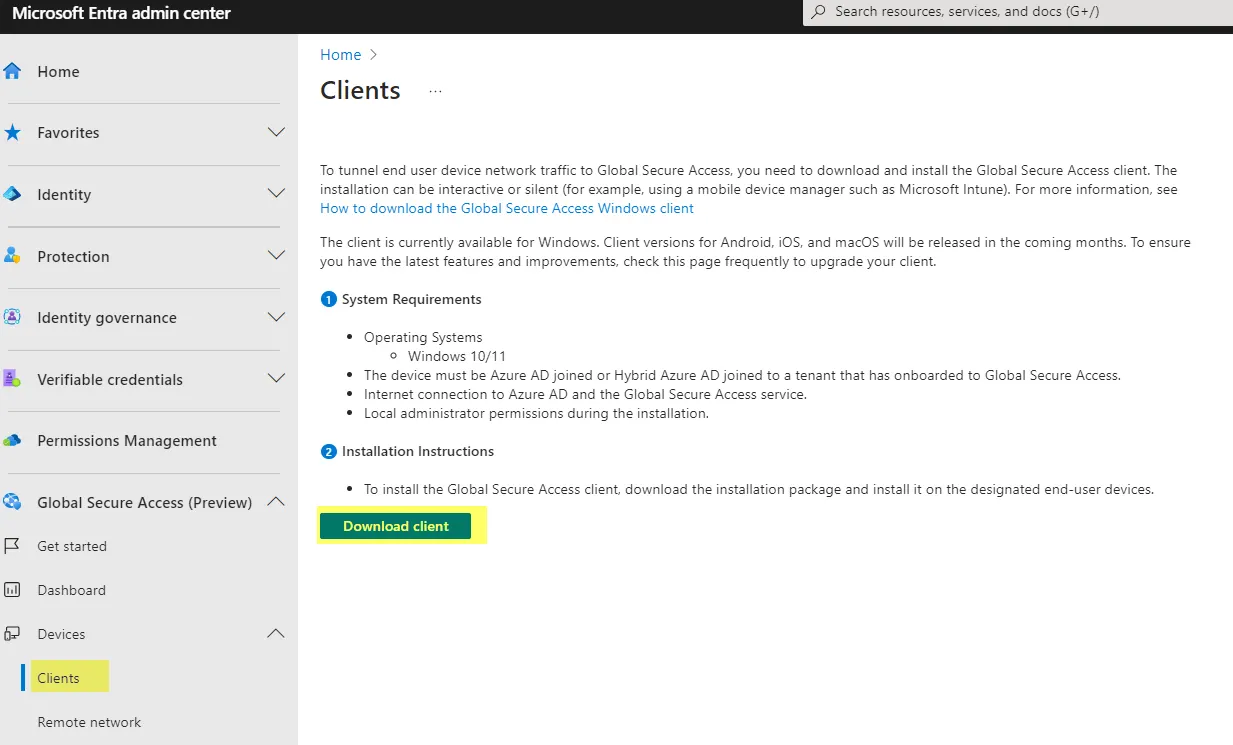
2. Download & install the Global Secure Access client
Install the client executable on any device and sign-in with your Entra ID account.
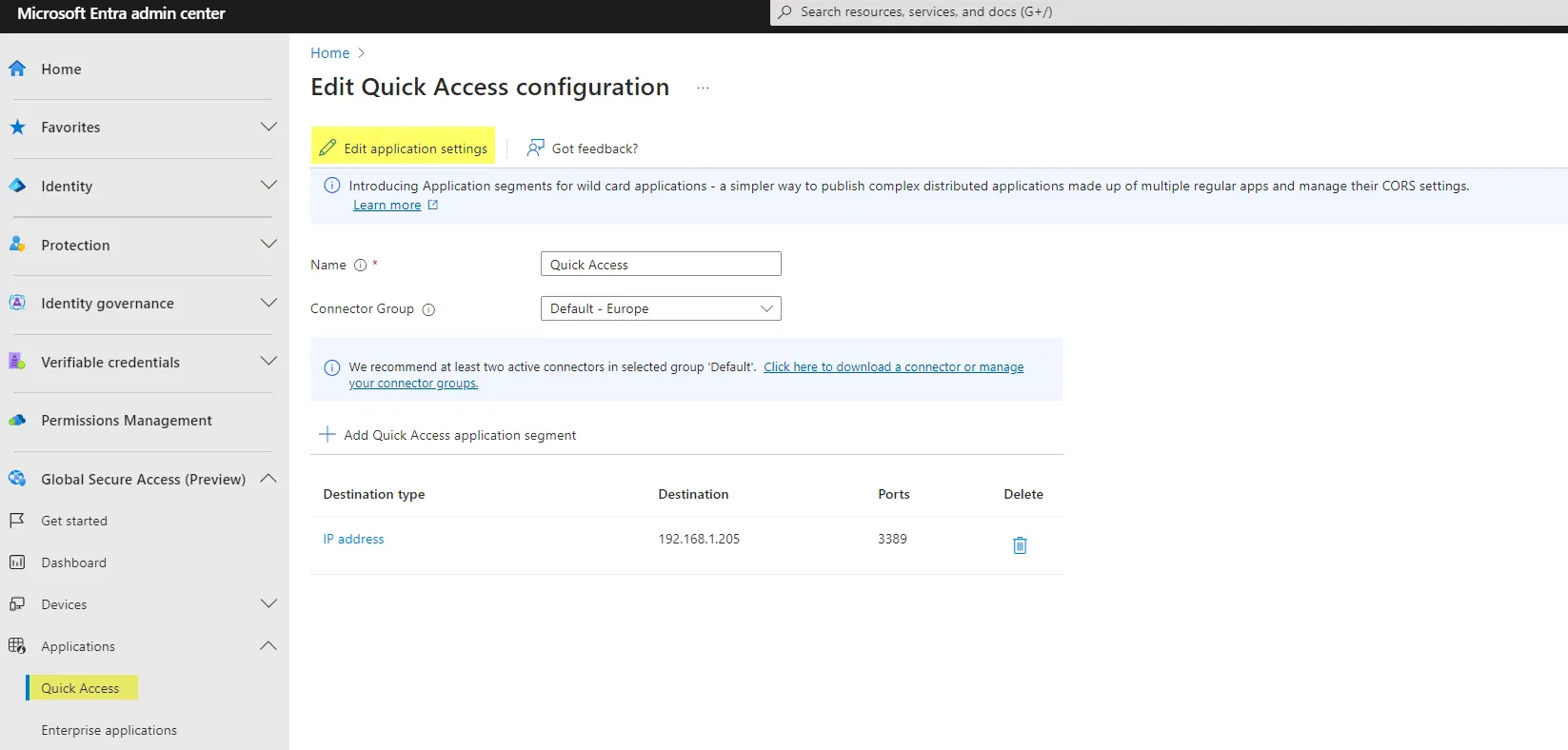
3. Configure Quick Access
Quick Access is an Enterprise Application in your tenant which is coming from Microsoft Entra SSE. As you can see, this is an Global secure access application, where a new tab of Network access properties is visible. What you specify here:
- Choose a (App Proxy) Connector group
- Add one or multiple entries for application segments / specify the IP or FQDN of any internal resource and the port (3389 for RDP, 445 for SMB)
4. Implement Conditional Access policy
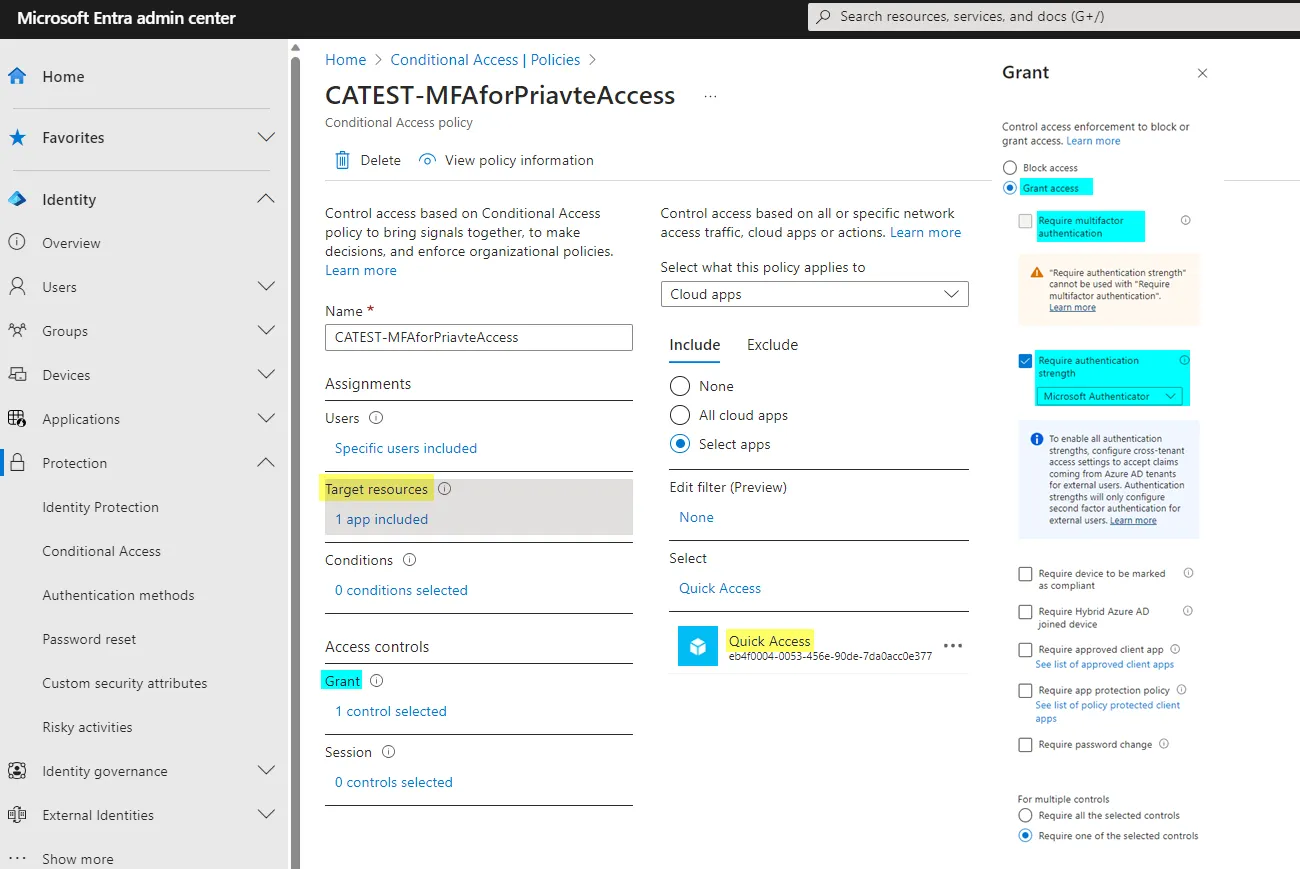
Create a new Conditional Access policy where you add the Quick Access app (this can also be renamed in the GSA segment) as target resource. Choose Grant access and select one of the controls. In my case I have added an Authentication strength to make sure MFA was not previously satisfied on my device.
Conclusion
From my perspective, Microsoft is expanding their identity portfolio with network tech to rise security and provide new features, which were until now reserved for other vendors.
For an organization with a single vendor and cloud strategy, this is a really welcome addition in their technology stack. Network traffic can now be a more than ever relevant source to controlling Internet Access to external resources with Entra ID, Enterprise app management and Conditional Access (and more). And for Private Access, this enables a whole new set of capabilities by integrating on-premises apps, resources and protocols to endpoints.
Microsoft Global Secure Access is a powerful addition in the Microsoft Cloud Security ecosystem.

powered by Oceanleaf



